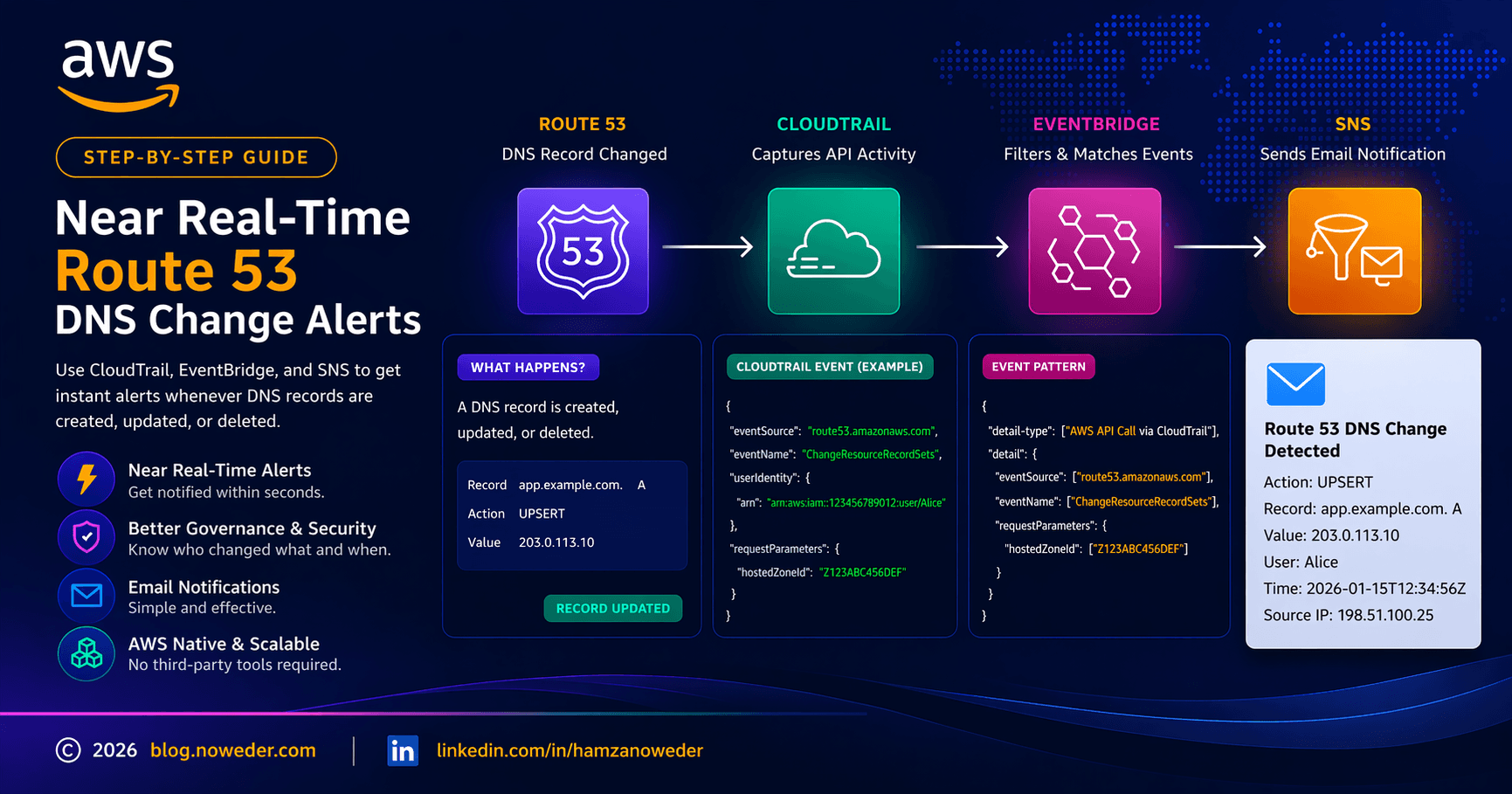
Building Near Real-Time Amazon Route 53 DNS Change Alerts on AWS
A Cloud Enthusiast
DNS changes are powerful and risky. A single incorrect Route 53 record can cause outages, security exposure, or compliance issues. A simple but effective governance control is to get alerted whenever a DNS record is created, updated, or deleted.
This guide walks through a repeatable, AWS-native pattern to implement near real-time alerts for Route 53 DNS record changes using CloudTrail, EventBridge, and SNS.
What this solution does
Detects any Route 53 DNS record change (CREATE, UPDATE, DELETE)
Works for public or private hosted zones
Provides visibility into:
Who made the change
Which record was modified
When and from where
Requires no agents and no third-party tools
Scales across accounts and organizations
High-level architecture
AWS CloudTrail captures Route 53 API calls
Amazon EventBridge filters DNS change events
Amazon SNS delivers notifications by email or other supported endpoints
Route 53 record changes are API calls using ChangeResourceRecordSets. CloudTrail is the authoritative source for these events.
Prerequisites
Before starting, ensure the following:
CloudTrail is enabled and logging management write events
You have permission to create:
EventBridge rules
SNS topics and subscriptions
You know the hosted zone ID you want to monitor
Important: Route 53 is a global service, so EventBridge rules for this use case should be created in
us-east-1.
Step 1: Verify CloudTrail is logging Route 53 changes
Open CloudTrail
Go to Event history
Filter by:
- Event source =
route53.amazonaws.com
- Event source =
Create or update a DNS record in Route 53
Confirm an event named
ChangeResourceRecordSetsappears
Open the event and note the exact value of:
requestParameters.hostedZoneId
Always use the exact value shown in CloudTrail.
Step 2: Create an SNS topic for notifications
Open Amazon SNS in
us-east-1Create a Standard topic
Create an email subscription
Confirm the subscription from your inbox
Test delivery by publishing a sample message to the topic.
Step 3: Create an EventBridge rule
Open Amazon EventBridge in
us-east-1Create a new rule
Select:
Event source: AWS events
Event type: AWS API Call via CloudTrail
Choose Custom pattern (JSON editor)
Use the following pattern and replace the hosted zone ID with your own:
{
"detail-type": ["AWS API Call via CloudTrail"],
"detail": {
"eventSource": ["route53.amazonaws.com"],
"eventName": ["ChangeResourceRecordSets"],
"requestParameters": {
"hostedZoneId": ["<HOSTED_ZONE_ID>"]
}
}
}
Why this pattern works
It filters CloudTrail API events reliably
It avoids over-filtering on unstable fields like the top-level
sourceIt captures all DNS record changes for the target hosted zone
Step 4: Configure SNS as the rule target
Set the EventBridge rule target to SNS
Select your SNS topic
Allow EventBridge to create or use its service role if required by your environment
In restricted environments, IAM permissions may need to be explicitly granted for EventBridge to create its invoke role and related policy.
Step 5: Test the solution
Create or delete a DNS record
Check:
EventBridge → Monitoring for matched events
Your email inbox for the SNS notification
You should receive an alert within seconds.
IAM considerations
In tightly controlled environments, especially AWS Organizations management accounts, you may hit IAM permission errors when EventBridge tries to create its service role and policy for SNS publishing.
Typical missing permissions include:
iam:CreateRoleiam:PassRoleiam:AttachRolePolicyiam:PutRolePolicyiam:CreatePolicyiam:GetPolicyiam:GetPolicyVersioniam:CreatePolicyVersioniam:DeletePolicyVersion
One practical approach is to allow EventBridge to create only the required invoke role and associated policy resources. Another option is to have the security team pre-create the role and policy for you.
Troubleshooting tips
1. No events matched in EventBridge
Check the following:
The EventBridge rule is in
us-east-1The rule is enabled
The event bus is
defaultThe event pattern uses the exact
hostedZoneIdvalue from CloudTrailThe rule is based on AWS API Call via CloudTrail
2. CloudTrail shows events but EventBridge does not match
Prefer filtering on:
detail.eventSourcedetail.eventName
Avoid relying too heavily on the top-level source field.
3. SNS is not delivering emails
Check:
The SNS subscription is confirmed
You can manually publish to the topic successfully
The EventBridge rule target is correctly configured
4. Email formatting is not clean
EventBridge input transformers have limitations, and SNS email delivery does not render string templates nicely with line breaks.
If you want:
Clean multi-line emails
Custom email subject
Better formatting
Support for multiple DNS record changes in a single request
Then use:
EventBridge → Lambda → SNS
Optional enhancements
Filter by action type
If you only want to detect specific actions, such as deletes, you can refine the filtering logic. For example, with a Lambda-based solution you can filter for:
CREATE
DELETE
UPSERT
Monitor multiple hosted zones
You can scale this design by either:
Creating one rule per hosted zone
Removing the hosted zone filter and handling routing or formatting logic in Lambda
Improve notification formatting
A Lambda function can:
Build a clean, multi-line email
Set a custom subject
Add severity levels
Handle multiple DNS changes in one request
When to use AWS Config instead
AWS Config is useful for:
Compliance monitoring
Configuration history
Drift tracking
CloudTrail plus EventBridge is better for:
Near real-time alerting
Operational visibility
Security monitoring
Final thoughts
This solution provides a lightweight, scalable, and repeatable way to monitor DNS changes across AWS environments.
It is especially valuable for:
Production environments
Security monitoring
Compliance and audit visibility
Once implemented, it becomes a low-effort, high-impact governance control that can be reused across many AWS accounts and organizations.